Another day, another phishing scam (or two)
As more and more people continue to work from home, we are seeing attackers leveraging social engineering tactics like phishing even more frequently, knowing that these teleworkers are typically not behind a corporate firewall that would likely block their malicious payloads. With that in mind, I received two emails today that highlight some of the ways that we can identify phishing and avoid becoming a statistic. Both emails appear to be from very different senders with very different approaches but, ultimately, with the same end game; get me to click on a malicious link.
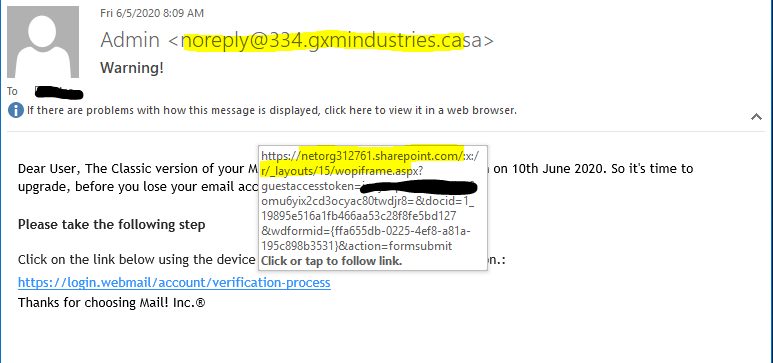
The sample below is a simple based email attempting to capitalize on the users fear that their email is about to go away and, if they don’t act fast, they will lose data. Note that the sender address is noreply@334.gxmindustries.casa , not at all familiar. Also note that, if we hover over the link (don’t click on it), the link to verify my email doesn’t go to anything that looks like an email link but goes to a SharePoint site and the very end has “&action=formsubmit“. Anytime that you receive an email telling you that ‘something’ is about to happen to your email, especially if it’s work-related, reach out to your IT department or IT Service Provider directly to confirm that the message is legitimate.
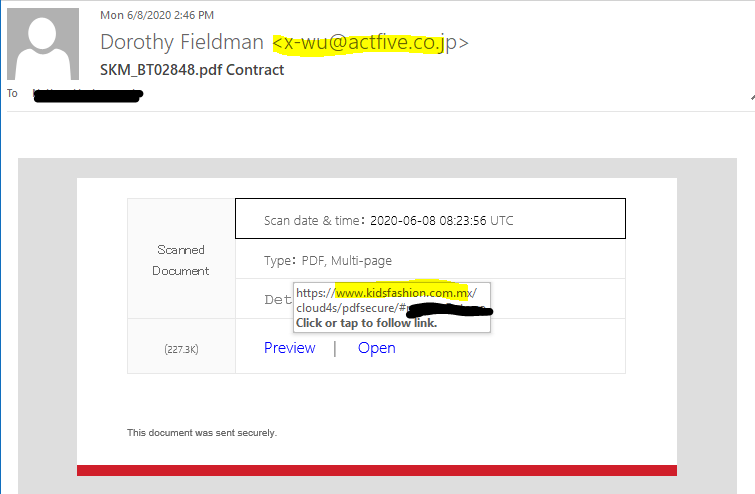
Similar to the previous email, this email is attempting to get the target to click on one of two links but, rather than leveraging fear, this is intended to look like an automated scan-to-email type message with the word ‘Contract’ subtly added to the subject (because that makes it look important). Like the previous email though, the sending email address x-wu@actfive.co.jp isn’t anything familiar to me and the link is going to something called www.kidsfashion.com.mx. Note the .mx top level domain there. The from address is .jp (Japan) and the email in the link ends in .mx (Mexico).
If you’re a business and you don’t have an IT Department or IT Service provider or if you aren’t happy with your current arrangement, we’d love an opportunity to earn your business.

